Securing the “Secure World”: How ProvenCore Leverages ARM TrustZone
As the Internet of Things (IoT) and Software-Defined Vehicles (SDV) expand, the need for hardware-level isolation has never been greater. ARM TrustZone technology provides the foundation by separating execution into a “Normal World” and a “Secure World”. However, the hardware is only as strong as the software running inside it.
The Role of a Verified Micro-Kernel
The “Secure World” requires its own operating system, one that is highly secure and verifiable. ProvenCore acts as this secure-world OS, providing a Trusted Execution Environment (TEE) for your most sensitive applications.
ProvenCore Isolation
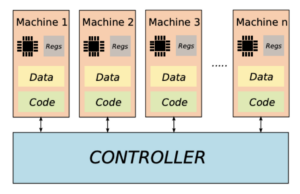
ProvenCore achieves hardware-level isolation through three distinct technical strategies:
- Minimal Trusted Computing Base (TCB): By using a micro-kernel architecture, ProvenCore keeps only the most critical services in privileged mode, running drivers and file systems as unprivileged services.
- Refinement Chain Proofs: The kernel’s security is proven through a chain of refinements, from the Security Policy Model (SPM) down to the Target of Evaluation Design (TDS), ensuring the final C code perfectly matches the abstract security goals.
- Access and Flow Control: A sophisticated system of “authorities” manages data copies and shared memory between processes, ensuring no unauthorized observation or tampering can occur.
Future-Proofing Critical Infrastructure
Whether it is managing Digital Rights Management (DRM) or protecting biometric credentials, ProvenCore ensures that processes run as if they were alone on the system. By leveraging the Proven Tools tool-chain, developers can now deploy high-assurance services with the confidence of mathematical certainty.